BACKGROUND
The importance of the key
The process of systematically scrambling text into a jumbled mess is referred to as encryption. While the reverse process of retrieving the original text from the scrambled text is called decryption. In both cases, a cryptographic key is used. This key is a piece of information, usually a string of numbers or letters that, when processed through a cryptographic algorithm, encrypts or decrypt data.
Therefore, to ensure that the data is not hacked by a third party, the secrecy of the key needs to be preserved. A key’s security strength is dependent on its mathematical algorithm, the size of the key, how the key is generated, and how secure is the process for both parties in the communication to define and agree which key to use.
This last problem on how the key is exchanged between parties is the problem that Quantum Key Distribution solves.
QKD in a nutshell
The concept of Quantum Key Distribution (QKD) allows the exchange of highly secure cryptography keys between two remote parties known in cryptography as Alice and Bob. The security of QKD relies on the laws of quantum mechanics by which quantum states cannot be cloned or copied. This means that an eavesdropper trying to look at the information encoded by Alice will irreversibly change their quantum properties letting Bob and Alice know that someone has tried to intercept the information.
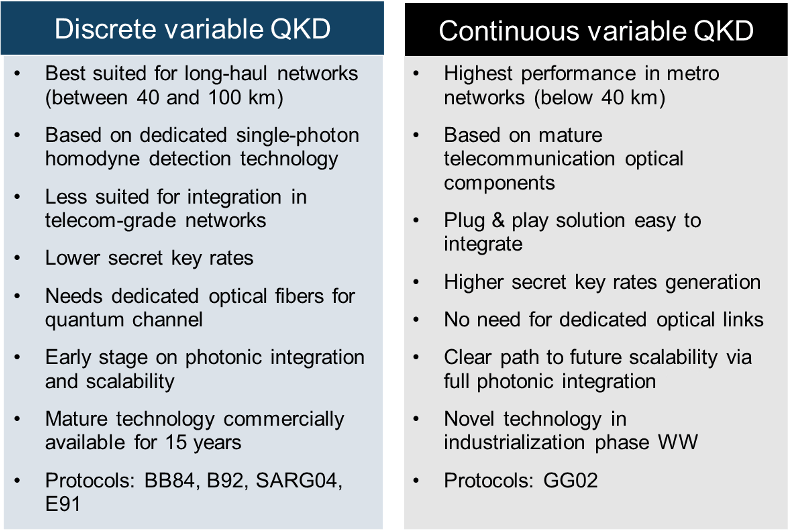
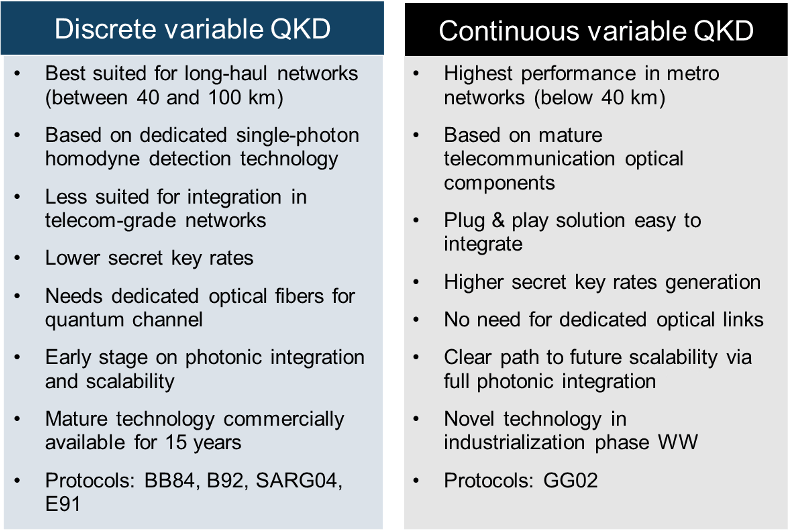
In general, there are two different approaches to QKD to generate the secret key: one was born in 1984 and focuses on particles of light (discrete variable QKD) while the other was conceived later on the early 2000s and looks at the wave nature of light (continuous variable QKD)
Discrete Variable QKD
In Discrete-Variable QKD (DV-QKD), the emitter (Alice) prepares and sends to the receiver (Bob) quantum signals, which consist of very weak single photons with encoded random data. The encoding is done following a specific QKD protocol by using a discrete-valued parameter of the photons (for example their polarization). Bob measures the state of the arriving photons by relying on a single-photon detector, and obtains data that is partially correlated to the data encoded by Alice. This data it will be used by Alice and Bob to distil a key using digital signal processing.
This version of QKD has been commercially available for over a decade now in the telecommunication industry with several manufacturers commercializing these systems across the world.
Continuous Variable QKD
In Continuous-Variable QKD (CV-QKD), the quantum signals typically consist of light with information encoded in the quadrature of its electromagnetic fields. Instead of single photon detectors, CV-QKD uses coherent homodyne or heterodyne detection to continuously retrieve the quadrature value of the light to distil the key. This is a much younger technology but it has developed rapidly and it is the core technology of LuxQuanta – in fact our vision sole provider.
Comparison between Discrete and Continuous variable QKD technologies
Performance comparison
The performance in terms of secret key rate between DV- and CV-QKD would largely depend on the electronic and optical components used to build the systems. Yet, there are some intrinsic characteristics of DV-QKD and CV-QKD that could influence the choice between the two technologies to be used in a network.
For instance, DV-QKD is in general more tolerant to channel losses. In CV-QKD, the signal-to-noise ratio rapidly decreases with channel losses, as data to generate the key are obtained for each transmitted quantum signal. Contrarily, in DV-QKD, the key is made of data obtained only from the received quantum signals. Hence, fibre demonstrations of DV-QKD have been possible over distances larger than those of CV-QKD.
Nevertheless, at short distances, CV-QKD allows for a key rate higher than DV-QKD as more than one secret bit per symbol could be extracted, and coherent detectors do not suffer from dead time present in single-photon detectors.
In addition, CV-QKD can be readily used in coexistence with classical communication in the same fibre by means of wavelength-division multiplexing making integration into existing networks less complicated.
Complementary technologies
Rather than competing, DV-QKD or CV-QKD are complementary technologies with different application spaces. Which one to use will depend on the fibre link characteristics, such as losses or power, and the number of available optical fibre channels.